Security Audit Checklist
Speichern, ausfüllen, drucken, fertig!
How to perform a professional Security Audit? How to create a Security Audit Checklist? Download this Security Audit Checklist template now!
Verfügbare Gratis-Dateiformate:
.pdf- Dieses Dokument wurde von einem Professional zertifiziert
- 100% anpassbar
Business Unternehmen checklist Checkliste Compliance Regelkonformität IT information technology Informationstechnologie Information Security Sicherheit Risk Risiko High Hoch Impact Auswirkung IT SOP Printable Checklist Druckbare Checkliste GDPR DSGVO Iso GDPR template DSGVO-Vorlage ccpa iso27001 isms ccpa template CCPA Vorlage nist standard iso it standard ISO-IT-Norm iso27001:2013 information security standards pdf Standards für Informationssicherheit PDF security standards definition Definition von Sicherheitsstandards network security standards Standards für die Netzwerksicherheit cyber security standards uk Cybersicherheitsstandards in Großbritannien cybersecurity Cybersicherheit cyber security compliance standards Beachtungsstandards für Cybersicherheit nist security standards information security standards Standards für die Informationssicherheit it security management IT-Sicherheitsmanagement information security best practices Bewährte Vorgehensweisen für die Informationssicherheit information security policy standards Standards für Informationssicherheitsrichtlinien it security IT-Sicherheit security techniques Sicherheitstechniken information security management systems Informationssicherheits-Managementsysteme cybersecurity standards Standards für Cybersicherheit IT compliance IT Regelkonformität it standard operating procedure IT-Standardarbeitsanweisung it security compliance Einhaltung der IT-Sicherheit how long does it take to implement iso27001 Wie lange dauert die Implementierung von ISO27001? iso27001 questions iso27001 Fragen iso 27001 controls list iso 27002 checklist ISO 27001 Kontrollliste ISO 27002 Checkliste cybersecurity audit checklist cybersecurity network audit checklist what is a cybersecurity audit checklist? soc audit checklist cybersecurity cybersecurity legal audit checklist nist cybersecurity audit checklist ip address audit checklist cybersecurity
How to perform a professional Security Audit? Are you looking for a professional Security Audit Checklist? If you've been feeling stuck or lack motivation, download this template now!
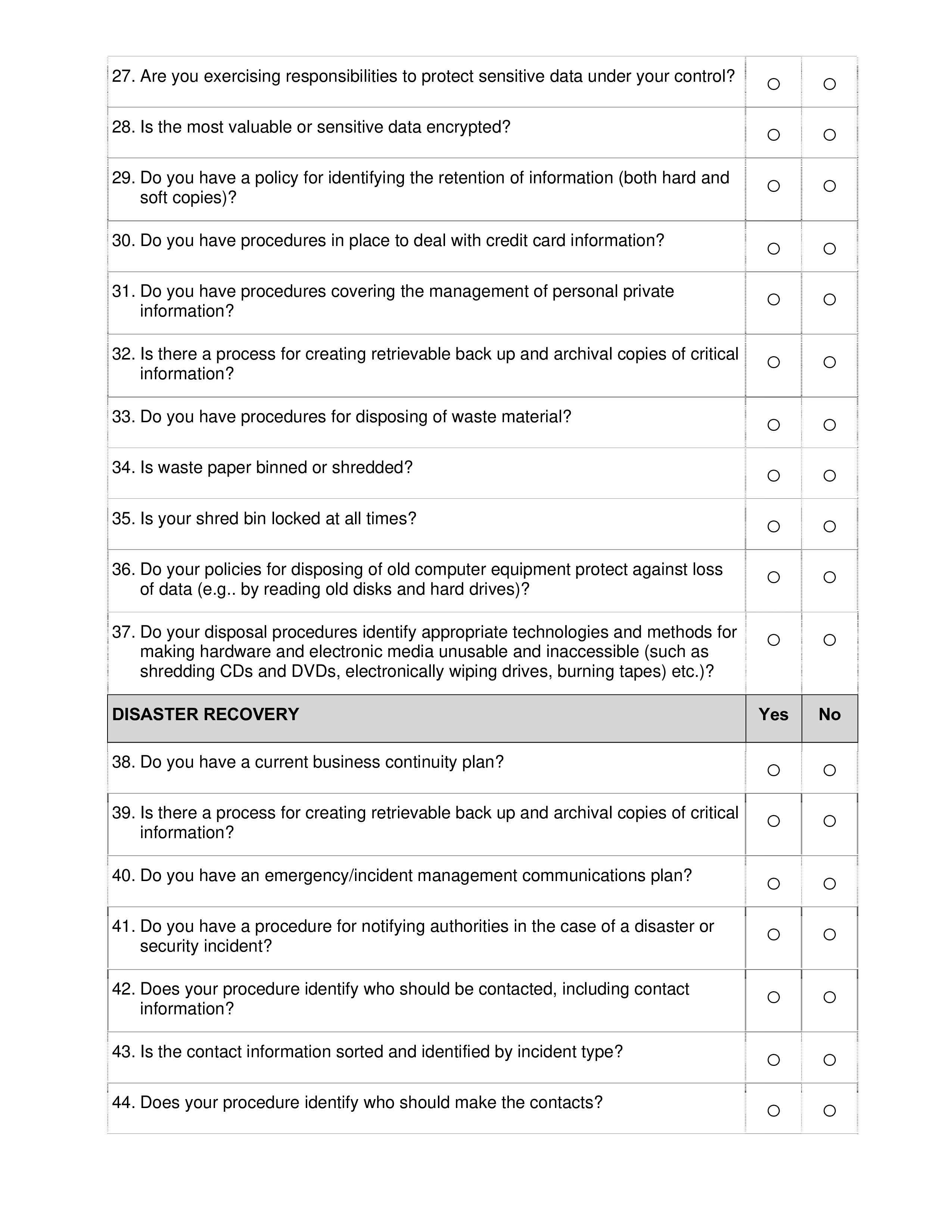
This Security Audit Checklist covers the most important topics that you are looking for and will help you to structure and communicate in a professional manner with those involved. There are several types of threats that may occur within an information system or operating environment Threats are usually grouped into general categories such as natural, human, and environmental, for example
NATURAL THREATS
Storm damage (e.g., flood) Fire Lightning strikes
HUMAN THREATS
Computer abuse Unauthorized access to Privacy Act and proprietary information Terrorism Sabotage or vandalism System tampering Spoofing Fraud Impersonation and social engineering Hacking Negligence or human error Theft Falsified data
ENVIRONMENTAL THREATS
Long-term power failure Chemical leakage Pollution The desired outcome of identifying and reviewing (assessing) threats and vulnerabilities are determining potential and actual risks to the organization.
Human Error
- Accidental destruction, modification, disclosure, or incorrect classification of information
- Ignorance: inadequate security awareness, lack of security guidelines, lack of proper documentation, lack of knowledge
- Workload: Too many or too few system administrators, highly pressured users
- Users may inadvertently give information on security weaknesses to attackers
- Incorrect system configuration
- Security policy not adequate
- Security policy not enforced
- Security analysis may have omitted something important or be wrong.
- Remediation Action Cost Benefit-Risk
Develop a foundation of Security Policies, Practices, and Procedures, especially in the area of Change Control Low High High 2 Establish and enforce a globally-accepted password policy Low High High 3 Address vulnerability results in order of high risk to low-risk
Establish an Operations group facilitated discussion to improve processes and communications, and to eliminate any misunderstandings
Establish router configuration security standards, forming baseline practices Low High High
Harden servers on the internal network Low High High No. Moderate to Expensive High
Feel free to download this intuitive template that is available in several kinds of formats, or try any other of our basic or advanced templates, forms or documents. Don't reinvent the wheel every time you start something new...
Download this Security Audit Checklist template and save yourself time and effort! You will see completing your task has never been simpler!
Besides this document, make sure to have a look at the IT Security Roadmap for proper implementation and this fit-for-purpose IT Security Kit here with over 40 useful templates. The document(s) are easy to modify and can be downloaded directly after purchase.
HAFTUNGSAUSSCHLUSS
Nichts auf dieser Website gilt als Rechtsberatung und kein Mandatsverhältnis wird hergestellt.
Wenn Sie Fragen oder Anmerkungen haben, können Sie sie gerne unten veröffentlichen.