IT compliance Page 2 templates
IT Compliance, in general, means conforming to a rule, such as a specification, directive, law, policy, or standards. IT Security Standards or similar regulatory compliance describes the goal that organizations aspire to achieve in IT security in their efforts to ensure that they are aware of and take steps to comply with relevant laws, policies, and regulations.
Due to the increasing number of regulations and need for operational transparency, organizations are increasingly adopting the use of consolidated and harmonized sets of compliance controls.[2] This approach is used to ensure that all necessary governance requirements can be met without the unnecessary duplication of effort and activity from resources. Some organizations keep compliance data—all data belonging or pertaining to the enterprise or included in the law, which can be used for the purpose of implementing or validating compliance—in a separate store for meeting reporting requirements. Compliance software is increasingly being implemented to help companies manage their compliance data more efficiently. This store may include calculations, data transfers, and audit trails. On our website you can find several kinds of laws, directives or standards that organizations can comply with, such as: the EU General Data Protection Regulation (GDPR), the California Consumer Privacy Act (CCPA), Cybersecurity standards, ISO 27001, DFARS (Defense Federal Acquisition Regulation Supplement), AVG, DoD, Federal Information Security Management Act (FISMA), Health Insurance Portability and Accountability Act (HIPAA), ISO 22301, ISO 22301:2012 IEC 27001,ISO/IEC 27001:2005, NEN ISO 27001, BS 7799-2, ISO/IEC 27031, ISO/IEC 27032, ISO/IEC 27701, NIST Cybersecurity Framework (CSF), etc.If you didn't start yet, you can find several plans on how to start implementing the necessary measures. We provide tools to help you become compliant.
We provide example Compliance document templates, that are easy to customize to your organization’s specific needs.
-
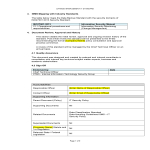
IT System Acquisition & Development
How to create an IT System Acquisition & Development Standard? Download this IT System Acquisition Standard if you are working on IEC, NIST, ISO27001:2013, etc
View template -
Change Management IT Cybersecurity Standard
How to create a Change Management CyberSecurity standard for your organization? Download this IT Security Standard now Standards and control objectives
View template -
IT Asset Management Cybersecurity Standard
How to create an IT Asset Management System for your organization? Download this IT Asset Management Standard if you are working on IEC, NIST, ISO27001:2013, or
View template -
Security Incident Management IT Standard
How to create a Security Incident Management Standard for your IT organization? Download this Security Incident Management if you are working on IEC, NIST, ISO2
View template -
Data Backup Plan
How to create a Data Backup Plan to improve your IT Security? Download this Data Backup Plan Standard if you are working on IEC, NIST, ISO27001:2013 or other IT
View template -
Cloud Computing IT Security Standard
Download this Cloud Computing CyberSecurity Standard if you are working on IEC, NIST, ISO27001:2013 or other IT and Cyber Security Standards and control objecti
View template -
Vulnerability Management IT Security Standard
How to create a Vulnerability Management IT Security Standard for your company? Download this Vulnerability Management CyberSecurity standard now.
View template -
End User Protection IT Standard
How to write an End-User Protection Standard? Download this End User Protection IT Standard if you are working on IEC, NIST, ISO27001:2013 or other IT and Cyber
View template -
IT Recovery Standard
How to create an IT Recovery Standard for your organization? Download this IT Recovery Standard if you are working on IEC, NIST, ISO27001:2013 or other IT and C
View template -
Logging and Monitoring IT Standard
Download this Logging and Monitoring IT Standard if you are working on IEC, NIST, ISO27001:2013 or other IT and Cyber Security Standards and control objectives.
View template
Latest topics
- Letter Format
How to format a letter? Here is a brief overview of common letter formats and templates in USA and UK and get inspirited immediately! - Google Sheets Templates
How to work with Google Sheets templates? Where to download useful Google Sheets templates? Check out our samples here. - Influencer Marketing Templates
What makes a good influencer? Check out our effective and useful Influencer Marketing Templates here! - House Cleaning Schedule Daily Weekly Monthly
Cleanliness is not just about what’s outside; it reflects what’s inside." Check out our House Cleaning Schedule Daily Weekly Monthly templates here. - Google Docs Templates
How to create documents in Google Docs? We provide Google Docs compatible template and these are the reasons why it's useful to work with Google Docs...